VM deployments using SSH
You can use a Secure Shell (SSH) deployment type to deploy your artifacts to VM or bare-metal hosts located in Microsoft Azure, AWS, or any platform-agnostic Physical Data Center (PDC).
Many traditional deployments use runtime environments such as Tomcat or JBoss. Your target hosts should have these installed before deployment. You can use the Harness Command step to install them in the same pipeline as your SSH deployment.
Deployment summary
An SSH deployment involves configuring the following:
- Create a Harness Secure Shell service.
- Set up a Harness connector to access your repository.
- Define the target infrastructure for deployment.
- Add the Harness connector for the target infrastructure.
- Add the credentials needed to connect to target hosts.
- Select the deployment strategy.
- Run the pipeline and review.
SSH stages
To start a SSH deployment, create a new pipeline and add a stage for Secure Shell deployments.
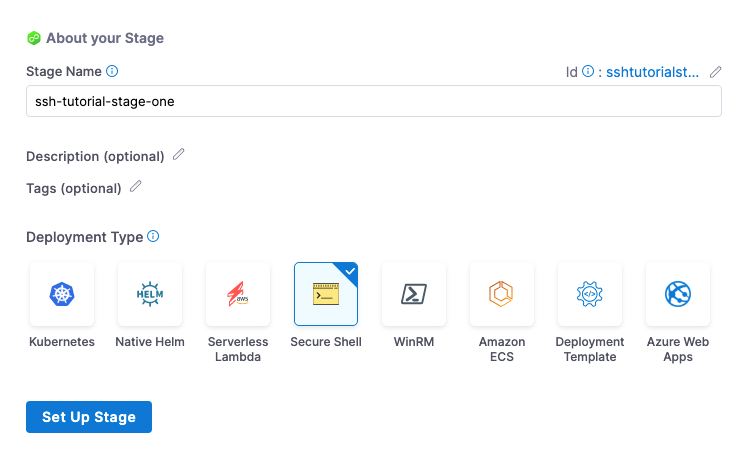
Next, you create the service, environment, and execution steps for the stage.
SSH Services
SSH Services define the artifact you want to deploy and any config files you want to use.
In the stage Service tab, you add the artifact metadata and the related config files to execute on the target hosts.
Create a Harness Secure Shell service
- For Select Service, select New Service, enter a name for the service.
- For Service Definition, in Deployment Type, select Secure Shell.
Add the artifact connector
For Secure Shell, you can access artifacts from the following sources:
- Jenkins
- Artifactory
- Bamboo
- Amazon S3
- Amazon ECR
- Nexus2
- Azure Artifacts
- GCR
- ACR
- Docker Registry (platform-agnostic)
- Custom. If you select Custom, you will need to provide a Bash script.
The supported artifact package types include Docker, JAR, TAR, WAR, RPM and ZIP.
Harness includes connectors for all the major artifact repositories. In this example, we will use Artifactory and a publicly available artifact.
In Artifacts, select Add Primary Artifact.
In Specify Artifact Repository Type.
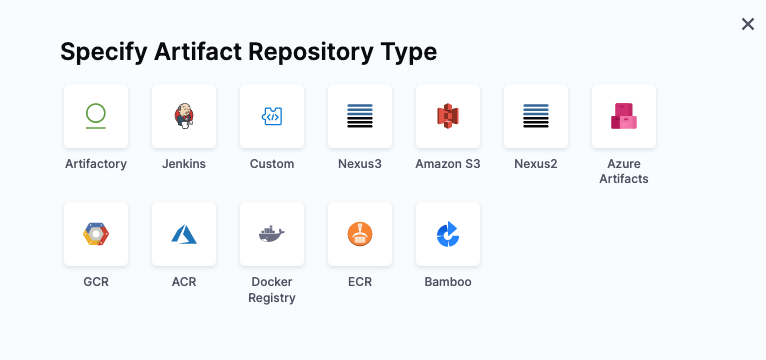
- As an example, select Artifactory and select Continue. You can use another artifact repo if you like.
For the Artifactory Connector, select New Artifactory Connector.
In Name, enter a name for the connector and select Continue.
In Details, enter the the following URL path for Artifactory Repository URL:
https://harness.jfrog.io/artifactory. In this example, we will use the artifacts stored in that repository.For Authentication, select Anonymous and select Continue.
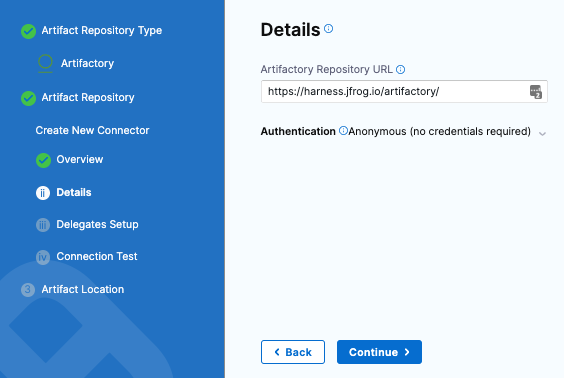
Select Continue to connect with Artifactory by using a Harness Delegate.
In Delegates Setup, select Connect through the Harness Platform.
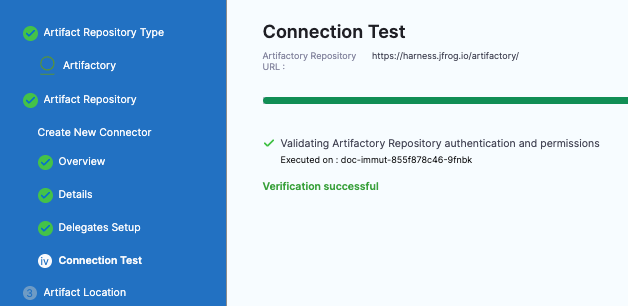
Select Save and Continue.
In Connection Test, Harness validates authentication and permissions for the repo.
Select Continue.
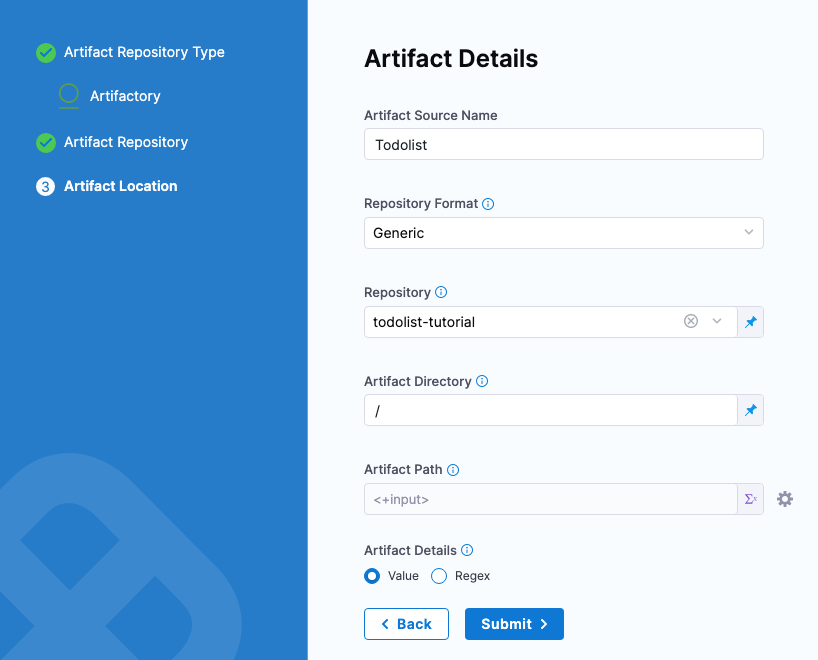
Set up artifact location and details
For this example, we'll use a publicly available ToDo List app artifact, todolist.war, available in a public Harness Artifactory repo.
In Artifact Details, enter the following:
In Artifact Source Name, enter Todolist.
In Repository Format, keep the default value Generic.
For Repository, enter: todolist-tutorial. Note that if you select Repository, Harness loads any available repositories and displays them for selection.
In Artifact Directory, enter a forward slash /.
In Artifact Details, keep the default Value.
In Artifact Path, leave the default Runtime Input value <+input> for that field.
Select Submit.
The artifact is added to your service.
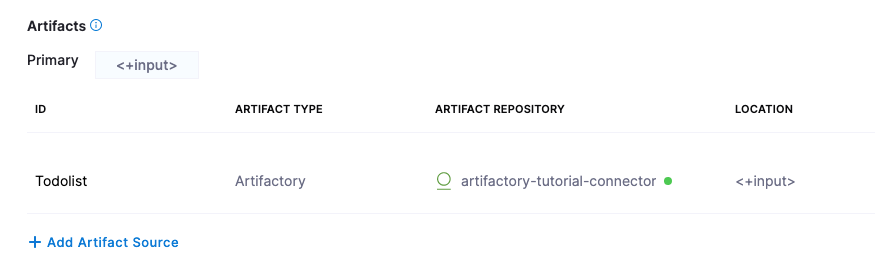
Select Save. The Service is added to your stage.
Select Continue to set up the target Environment.
SSH Environments
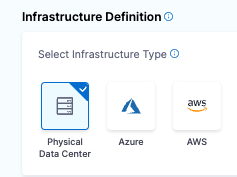
In the stage Environment section, you define the infrastructure definition for the target hosts.
Add the target infrastructure
In Specify Environment, select New Environment and enter a name.
For Environment Type, select Pre-**Production, and select Save**.
For Specify Infrastructure, select New infrastructure.
Enter a name for the new infrastructure.
For Select Infrastructure Type, select where you want to deploy. For this example, we'll use Physical Data Center.
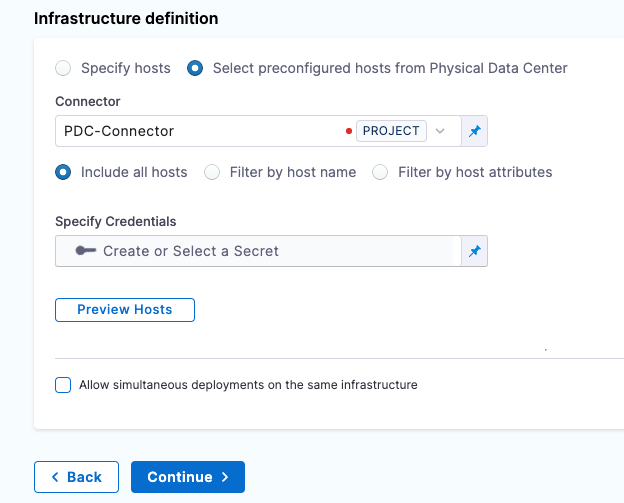
- Keep the default selection: Select preconfigured hosts from Physical Data Center.
Create the PDC connector for the hosts
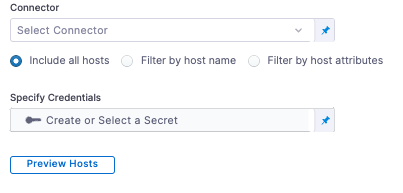
In Infrastructure Definition, for Connector, select Select Connector to create the Connector for PDC.
In Create or Select an Existing Connector, select New Connector.
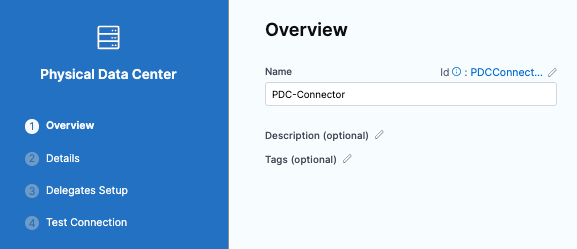
In Physical Data Center, enter a name for this connector: PDC-Connector.
Select Continue.
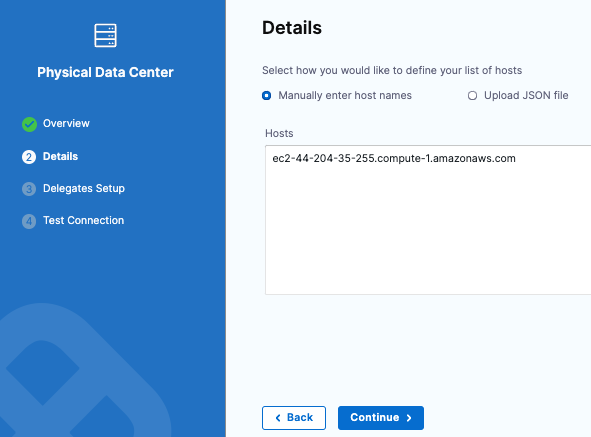
In Details, keep the default for Manually enter host names and enter the hostname for the EC2 instance.
Select Continue.
In Delegates Setup, keep the default for Use any available Delegate.
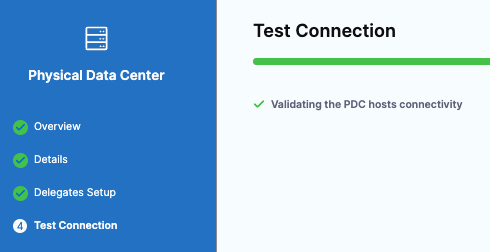
Select Save and Continue. Harness validates connectivity for the PDC connector.
Select Finish. The Infrastructure Definition is updated with the PDC Connector.
Use an SSH credential for authenticating to the target hosts
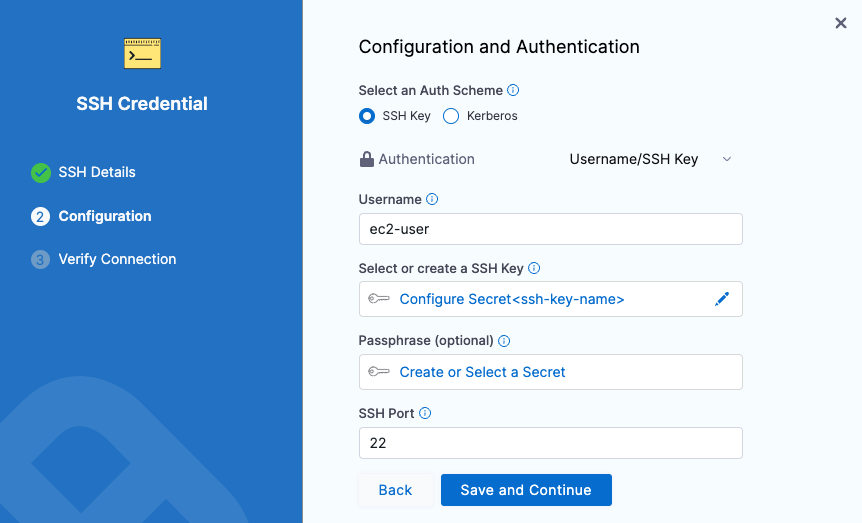
You can use an SSH Key or Kerberos for authenticating to the target host. In this tutorial, we will use an SSH Key.
In Specify Credentials, select Create or Select a Secret.
In Create or Select an Existing Secret, select New SSH Credential.
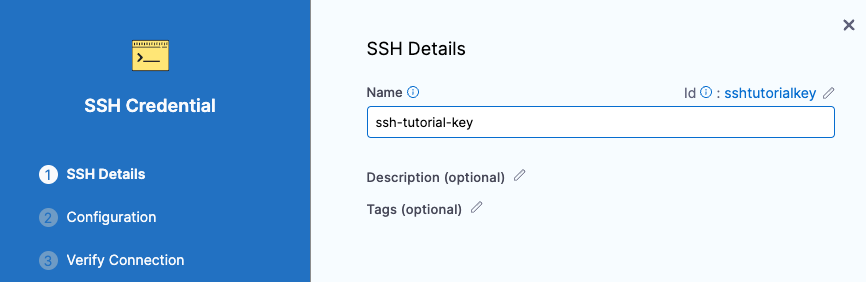
In SSH Details, for Name, enter a name for this SSH Credential and select Continue.
In Configuration and Authentication, you have three authentication options: In this example, we will use Username/SSH Key. Select the down-drop menu and select Username/SSH Key.
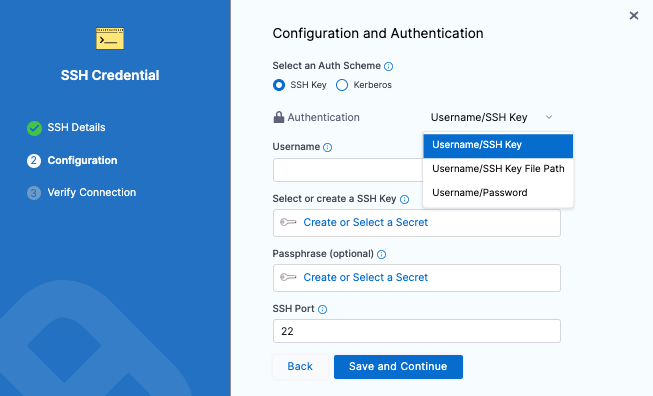
For username, enter ec2-user. This is the user for the EC2 instance.
For Select or create a SSH Key, select Create or Select a Secret.
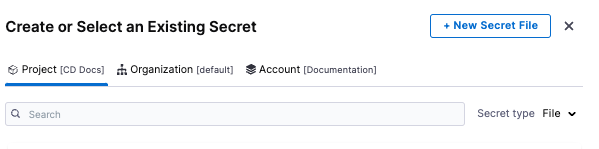
in Create or Select an Existing Secret, select New Secret File.
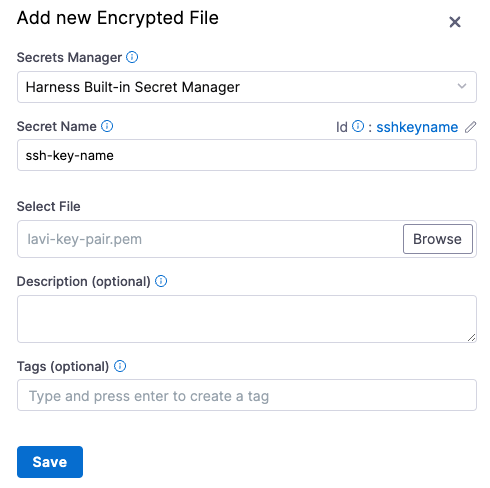
in Add new Encrypted File, enter a name for Secret Name: ssh-key-name. This is the name you will use to reference this file.
For Select File, select Browse. On your machine, browse for the .pem file that you downloaded from your EC2 instance. Select that file and Harness uploads it to the Select File field.
Select Save.
In Configuration and Authentication, keep the default values for Passphrase and SSH port. Select Save and Continue.
In Verify Connection, enter the hostname for the EC2 instance in the Add a Host Name to start verification field and select Connection Test.
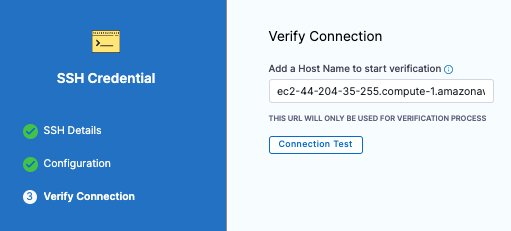
The Secure Shell connection to the EC2 instance is tested. Select Finish. Select Continue.
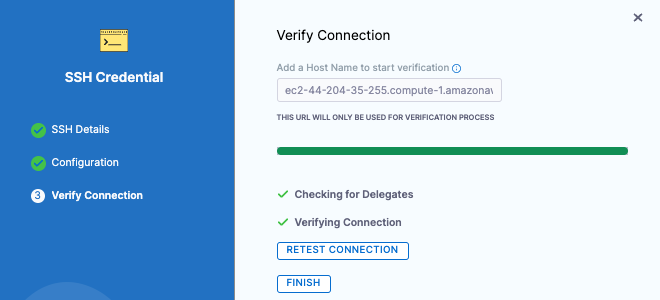
You can use the Preview Hosts section to test the connection at any time.\
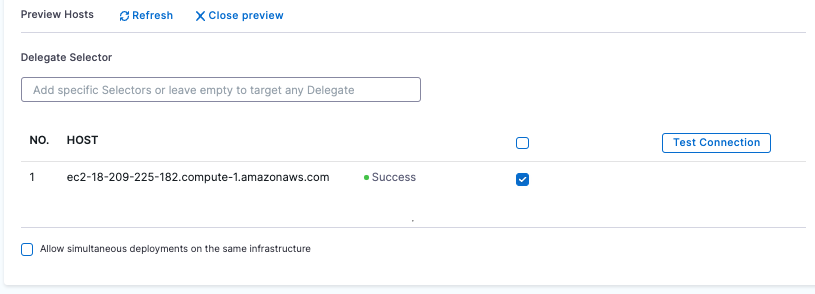
Select Save.
Back in Environment, select Continue.
Next, you'll select the deployment strategy for this stage, the package type, and the number of instances to deploy on.
SSH Executions
In Execution, Harness automatically adds the steps required to deploy the service to the environment according to the deployment strategy you select.
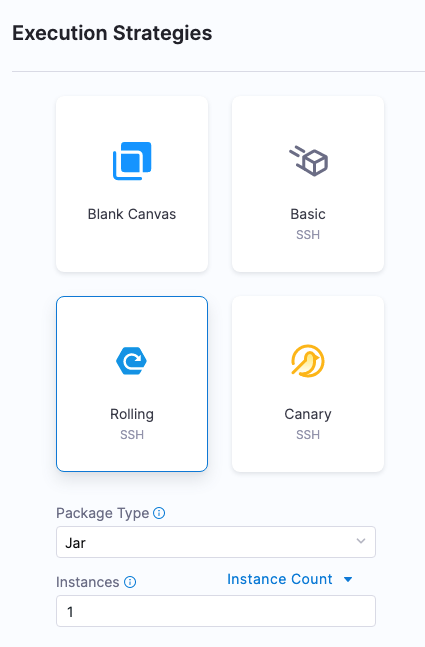
The Execution Strategies supported for Secure Shell include Blank Canvas, Basic, Rolling, and Canary. Let's look at Basic.
Basic deployments
In Execution Strategies, select Basic. Typically, you use basic when deploying to one host and rolling or canary for multiple hosts.
For Package type, select WAR.
Select Use Strategy. Harness adds the Deploy step for execution.
Select the Deploy step. Here is where you add the scripts for your package. We'll use the defaults for this example. So, we'll simply copy the artifact to the target host.
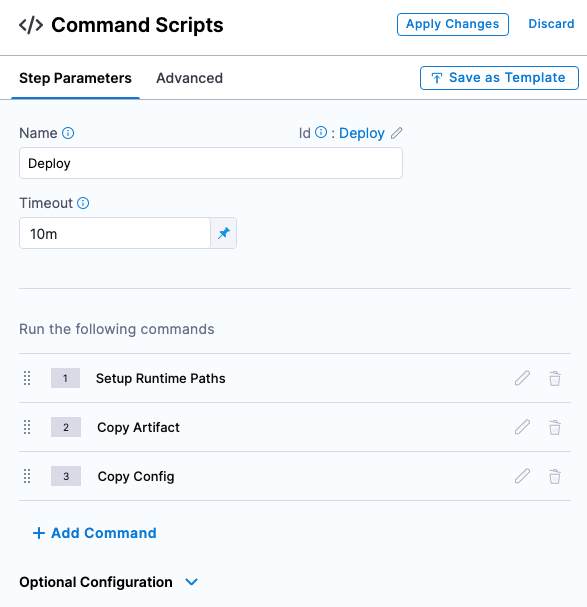
In Command Scripts, edit Copy Config.
In Edit Command, for Select file type to copy, select Artifact.
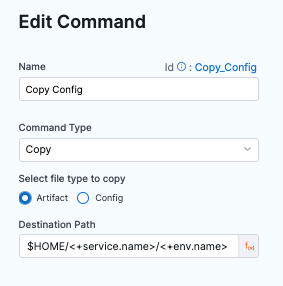
Select Save.
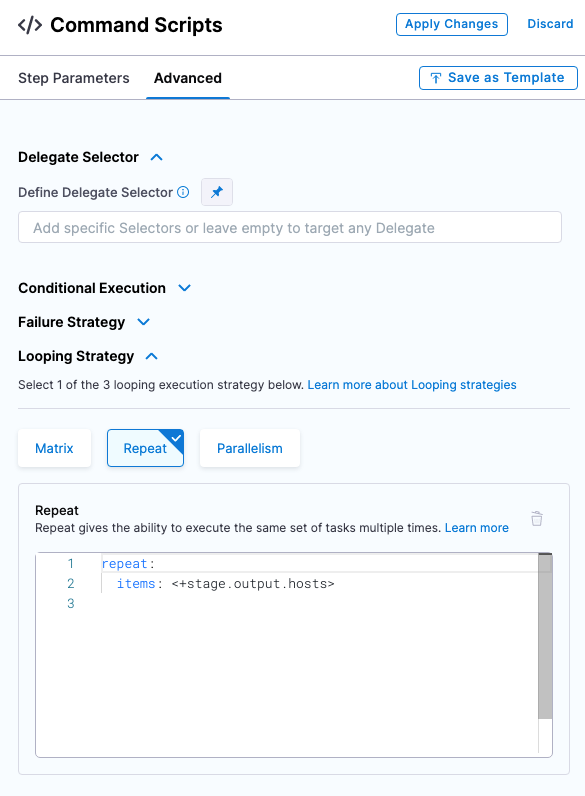
Review Looping Strategy: the looping strategy repeats deployments for multiple hosts and for different deployment strategies (Basic, Rolling, Canary).
- Select Advanced.
- Select Looping Strategy. You can see that the step will be repeated for all hosts using the
<+stage.output.hosts>expression.
For example, if you had two hosts the step would be repeated for each host.
Select Apply Changes.
When you're done, select Save to publish the Pipeline.
Deploy and review
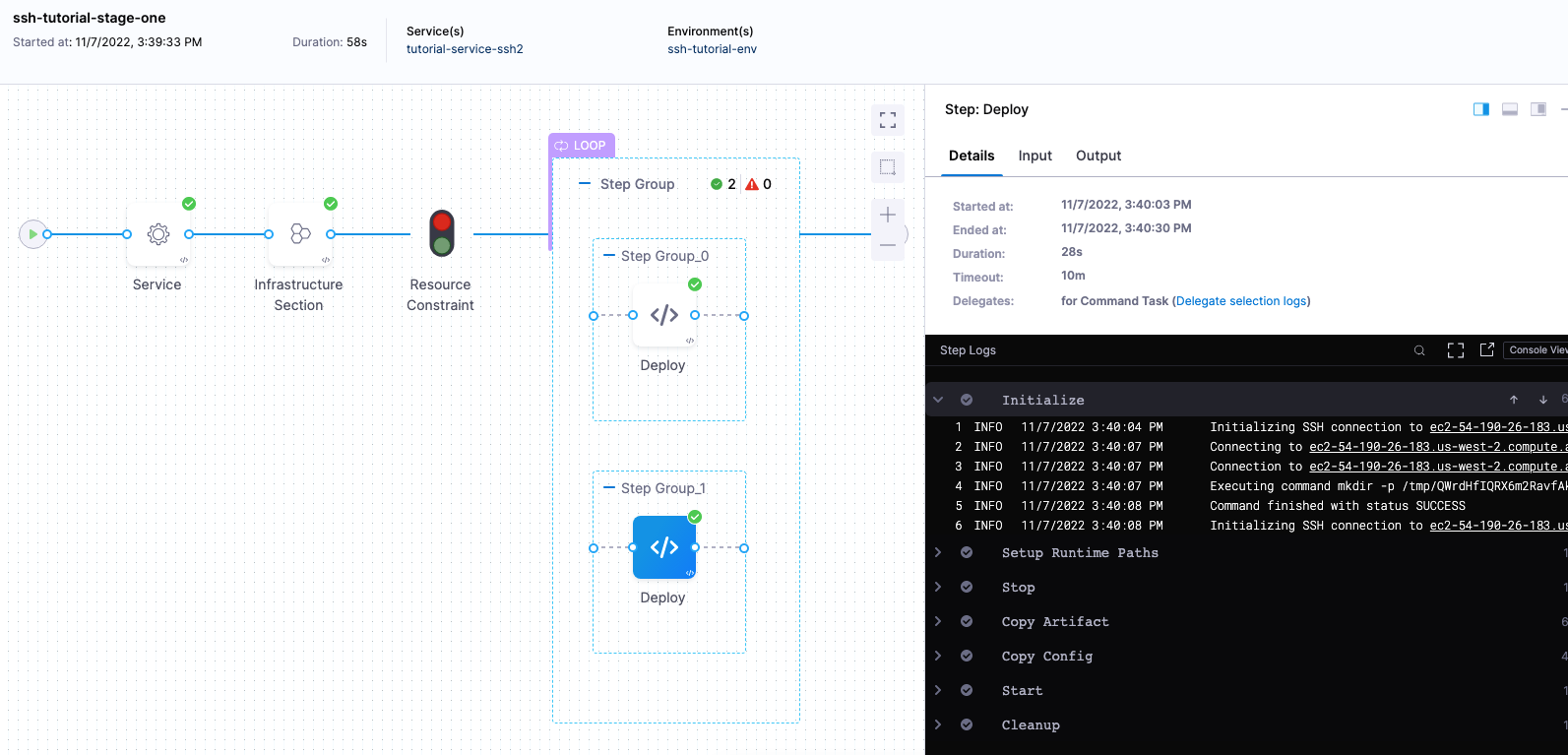
Let's look at an example SSH deployment.
Select Run to run the pipeline.
In Run Pipeline, for Primary Artifact, select Todolist.
In Artifact Path, Harness displays a list of available artifact packages.
Select todolist.war.
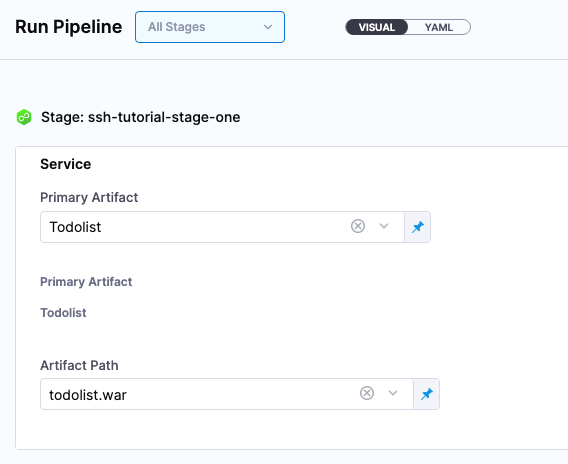
Select Run Pipeline. Harness runs the pipeline and the Console View displays the tasks executed for each step.
Review deployment
Let's review what is happening in the Deploy step. Most sections correspond to the commands you can see in the Deploy step.
- Initialize: initialize the connection to the host(s) and create a temp directory for the deployment.
- Setup Runtime Paths: create folders for runtime, backup, and staging.
- Copy Artifact: copy the artifact to the host.
- Copy Config: copy the config files (if any) to the host.
- Cleanup: remove temp directories.
Initialize
Initializing SSH connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connecting to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com established
Executing command mkdir -p /tmp/aCy-RxnYQDSRmL8xqX4MZw ...
Command finished with status SUCCESS
Initializing SSH connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connecting to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Setup Runtime Paths
Initializing SSH connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connecting to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com established
Executing command...
Command finished with status SUCCESS
Copy Artifact
Filename contains slashes. Stripping off the portion before last slash.
Got filename: todolist.war
Connecting to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com established
Begin file transfer todolist.war to ec2-54-201-142-249.us-west-2.compute.amazonaws.com:/home/ec2-user/tutorial-service-ssh2/ssh-tutorial-env
File successfully transferred to ec2-54-201-142-249.us-west-2.compute.amazonaws.com:/home/ec2-user/tutorial-service-ssh2/ssh-tutorial-env
Command finished with status SUCCESS
Copy Config
Filename contains slashes. Stripping off the portion before last slash.
Got filename: todolist.war
Connecting to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com established
Begin file transfer todolist.war to ec2-54-201-142-249.us-west-2.compute.amazonaws.com:/home/ec2-user/tutorial-service-ssh2/ssh-tutorial-env
File successfully transferred to ec2-54-201-142-249.us-west-2.compute.amazonaws.com:/home/ec2-user/tutorial-service-ssh2/ssh-tutorial-env
Command finished with status SUCCESS
Cleanup
Initializing SSH connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connecting to ec2-54-201-142-249.us-west-2.compute.amazonaws.com ....
Connection to ec2-54-201-142-249.us-west-2.compute.amazonaws.com established
Executing command rm -rf /tmp/aCy-RxnYQDSRmL8xqX4MZw ...
Command finished with status SUCCESS
Congratulations! You have now successfully created and completed the steps for running a pipeline by using Secure Shell.
Notes
Selecting multiple hosts
You can add multiple hosts in the Physical Data Center Connector:
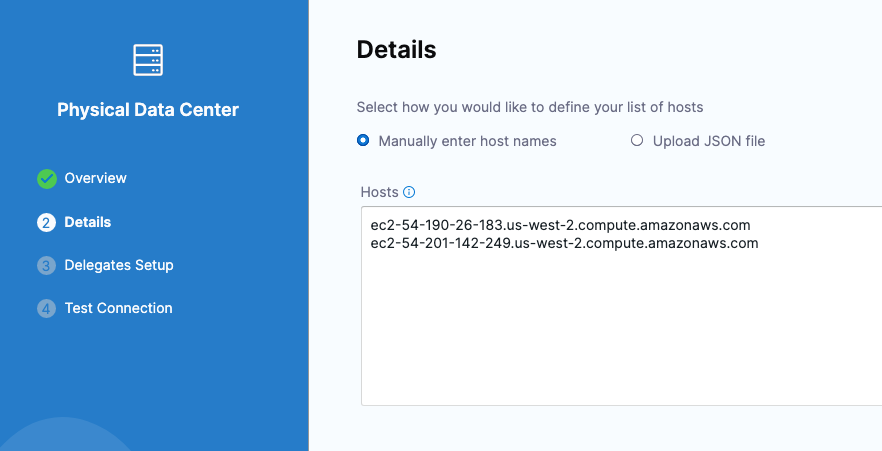
During deployment, you'll see each host listed in the loop:
Looping strategies for each deployment strategy
Only the Repeat Looping strategy is supported by the Command step. Also, only the items parameter is supported when running the Command step on multiple target hosts:
repeat:
items: <+stage.output.hosts>
The Repeat looping strategy is used differently for the basic, rolling, and canary deployment types.
The looping strategy is automatically added to the Deploy step and configured for the deployment type you selected:
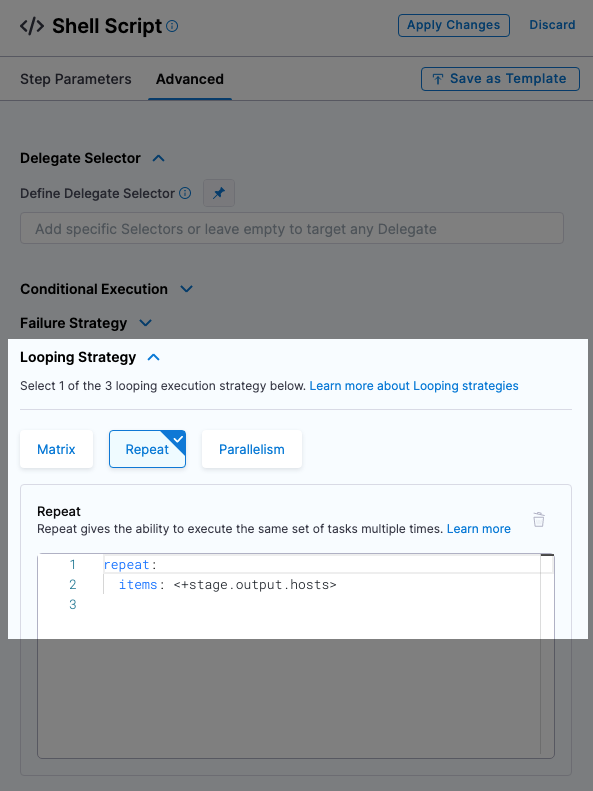
Let's look how it's used for different deployment types.
Basic
The looping strategy for the basic deployment simply repeats the deployment on all the target hosts.
repeat:
items: <+stage.output.hosts>
Rolling
For a rolling strategy, you specify how many instances you want to deploy per phase.
Let’s say you have 10 target hosts in the stage Infrastructure Definition and you want to have 3 instances per phase.
In Instances, you would enter 3.
As a result, when execution starts there will be 4 phases: 3, 3, 3, 1. The number of instances per phase can be provided as a count or a percentage.
This is an example of the rolling strategy using 2 hosts with 50% in Instances.
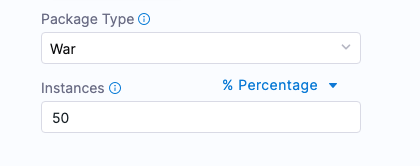
This means, that Harness will roll out to 50% of target hosts first, and then the remaining 50% if the first 50% were successful.
Harness creates 2 phases.
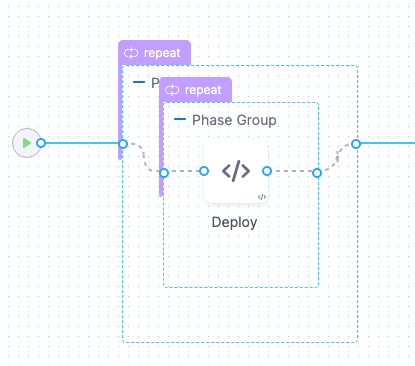
You can add any Approval steps inside the Phase Group. For more information, go to Approvals.
The looping strategy for the first phase deploys to 50% of the hosts (partitions):
repeat:
items: <+stage.output.hosts>
maxConcurrency: 1
partitionSize: 50
unit: Percentage
The looping strategy for the second phase repeats the partition count:
repeat:
items: <+repeat.partition>
The <+repeat.partition> expression resolves how many instances (items) to iterate over per one partition (phase).
Let’s say we have 10 hosts and 4 partitions organized as 3, 3, 3, 1. The first partition includes 3 hosts, the second and third each have 3, and the last one has 1 host.
So, partition1 = host1, host2, host3, partition2 = host4, host5, host6, partition3 = host7, host8, host9, and partition4 = host10.
Canary
For canary strategies, Harness calculates phase instances based on the number of hosts and the number of requested instances per phase.
Let’s say you have 10 hosts and you add 2 phases with 50% and 100%. This means Harness deploys on 5 instances in the first phase and on the rest of the instances in the second phase.
Here is an example of the Canary strategy using 2 hosts and 2 phases. The first phase deploys to 50% and the second phase deploys to 100%.
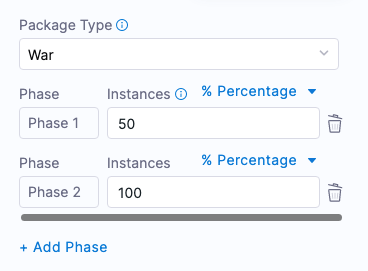
This means, that Harness will roll out to 50% of target hosts first, and then the remaining 50% if the first 50% were successful.
Harness creates 2 phases as step groups.
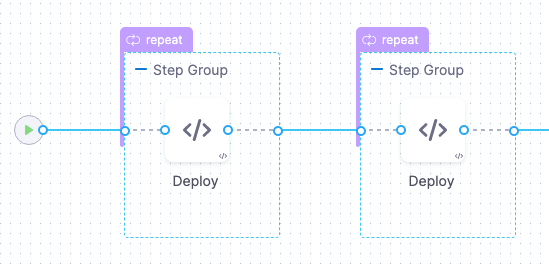
You can add any Approval steps between the Step Groups. See Adding ServiceNow Approval Steps and Stages, Adding Jira Approval Stages and Steps, and Adding ServiceNow Approval Steps and Stages.
The Looping Strategy for the first Phase selects 50% of the target hosts:
repeat:
items: <+stage.output.hosts>
start: 0
end: 50
unit: Percentage
The Looping Strategy for the second Phase starts at the 50% from the first phase and continues to 100%:
repeat:
items: <+stage.output.hosts>
start: 50
end: 100
unit: Percentage
Reference hosts in steps using expressions
You can use all of the <+instance...> expressions to reference your hosts.
For Microsoft Azure, AWS, or any platform-agnostic Physical Data Center (PDC):
<+instance.hostName><+instance.host.hostName><+instance.name>
For Microsoft Azure or AWS:
<+instance.host.privateIp><+instance.host.publicIp>
instance.name has the same value as instance.hostName. Both are available for backward compatibility.
For more details, go to Built-in and custom Harness variables reference.